Scene 4 (The Gap)
But even if fraud and breach statistics were combined into one comprehensive database, I’d still have a problem.
Most cybercrime never gets reported at all.
The Department of Justice estimates that only 1 in 7 cybercrimes are reported; meaning roughly 85% of incidents remain invisible.1 Recent research reveals the scope is even worse: 81% of cybersecurity managers admit at least one material cyber incident went unreported to leadership in the past year, with 30% saying 2-4 incidents went unreported.2 Even more troubling, 8% of cybersecurity leaders admitted they or a teammate intentionally did not report a cyber incident for fear of job loss.3
Security leaders cite the top three reasons for not reporting as: concerns about reputational or regulatory fallout (44%), the belief the incident could be contained internally (41%), and the lack of safe reporting protocols (37%).4 A 2023 Keeper Security study showed 41% of incidents aren’t even reported internally, and 48% aren’t reported to authorities.5
The entire security industry: the threat intelligence reports, the DBIR statistics, the APT profiles I’d been reading, all of it was built on maybe 10-15% of actual cybercrime data!
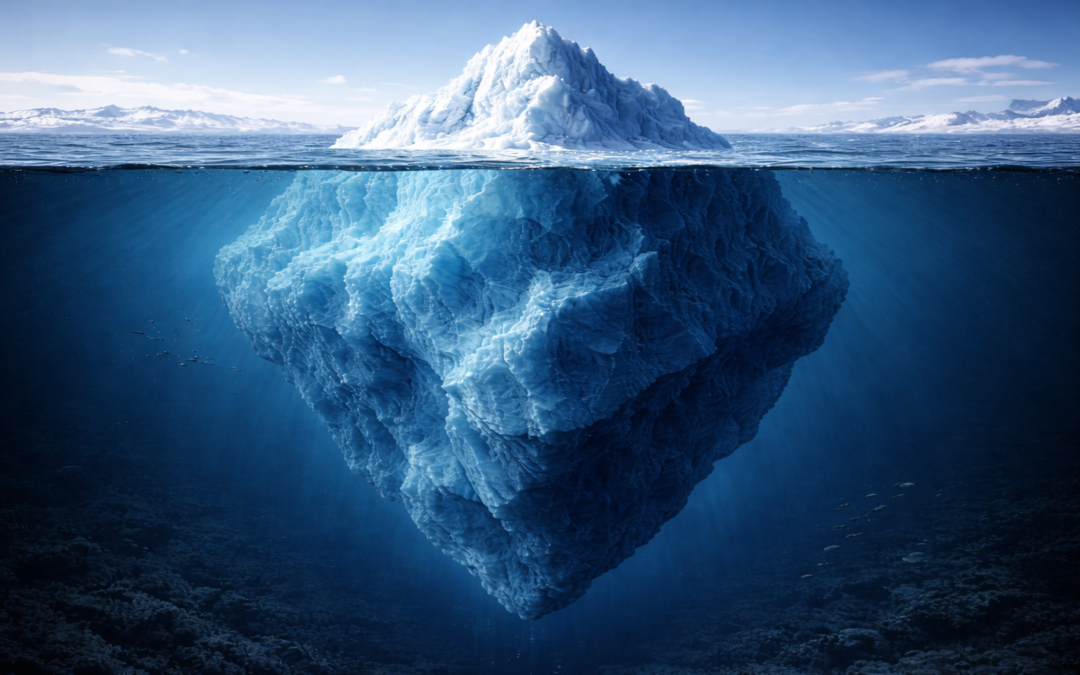
We were building threat models on the visible sliver of a mostly hidden iceberg.
I thought about my own work. That movie clip vulnerability I’d found; the one where you could enumerate an entire film catalog, create unlimited clips through an unauthenticated API, and programmatically capture complete movies before they were officially released. No rate limiting. Predictable public storage URLs. CSRF amplification possible.
Technically impressive, maybe, I think so. Creatively chained. It absolutely required understanding the business logic of the clip approval workflow.
But would it ever show up in breach statistics if exploited?
No. It’s content theft, not data breach. No PII exposed, no breach notification required. The company might not even realize it happened until pirated copies showed up online. And even if they caught someone, they’d handle it as intellectual property theft or a contractual violation, not a “security incident.”
This was the pattern. Business logic vulnerabilities that enable fraud, insider threats, policy abuse, content theft, all of it happens in the shadows. Reported to legal departments, HR, fraud teams, copyright enforcement. Never to the security teams publishing statistics.
I couldn’t prove business logic vulnerabilities mattered because most of what happens never gets documented as a security incident in the first place.
“Think of the dark figure of crime like the hidden part of an iceberg. The crimes recorded by police are just the visible tip, while beneath the surface lies a much larger mass of crime that stays invisible.”6
Scene 5 (The Realization)
I’d spent weeks researching. APT groups, fraud statistics, reporting gaps, enterprise applications. Hours diving into threat intelligence reports, payment network data, breach disclosure databases.
And I still couldn’t answer my original question: Are business logic vulnerabilities actively exploited by threat actors?
The problem wasn’t lack of effort. The problem was the question couldn’t be answered with the data that exists.
I had to accept three uncomfortable truths.
First: Some questions are inherently unknowable. Take that $89 billion in first-party fraud. How much was technical exploitation versus social engineering? The data doesn’t exist. Payment processors track what happened (chargebacks, promo code abuse, refund fraud) but not how. A customer who sweet-talks a cashier into stacking incompatible coupons shows up in the same fraud statistics as one who exploits a race condition in the discount workflow. The industry doesn’t distinguish because fraud prevention focuses on detecting fraud, not classifying attack vectors.
Second: Some questions I searched for but found nothing. Forty APT groups, hundreds of documented campaigns, zero business logic exploitation. But this only represents the attackers who got caught. The successful ones, the ones who exploited business logic so cleanly they were never detected, wouldn’t appear in any threat intelligence report. The published attacks are the ones that made enough noise to warrant investigation and disclosure. Absence of evidence isn’t evidence of absence. It’s just evidence of what gets documented.
Third: Some data exists but is inaccessible. Enterprise applications (Human Capital Management (HCM) systems, B2B SaaS platforms) hide exploitation behind NDAs, private bug bounty programs, and confidential SOC 2 audits. The only publicly documented breach I could find was Kronos, and that was ransomware, not business logic. When a business logic flaw gets exploited, but no PII is exposed, there’s no breach notification requirement. The vulnerability gets patched quietly. The exploitation never makes it into any database I could search.
I needed a framework for intellectual honesty. For each assertion, I had to ask: Do I have data? Did I search for it? Could it theoretically exist? Or is it fundamentally unanswerable with current industry practices? Some questions had clear answers. Some had documented absences. Some hit access barriers I couldn’t get past. And some were unknowable by design.
Weeks of research, and I couldn’t prove business logic vulnerabilities were actively exploited at scale.
But staring at my notes, I realized something.
I’d been asking the wrong question the entire time.
The question wasn’t “Are business logic bugs exploited?” The question was “What’s the ROI of finding low-probability, high-skill vulnerabilities versus automating detection of high-probability, low-skill ones?”
And that question I could answer.
“The most serious mistakes are not being made as a result of wrong answers. The true dangerous thing is asking the wrong question.” – Peter Drucker7
Return to the Pentester’s Guide to AI Disruption: A 6-Part Series
- U.S. Department of Justice (2018 data, cited in Cybersecurity Ventures 2024 Almanac), https://cybersecurityventures.com/cybersecurity-almanac-2024/ ↩︎
- Viking Cloud, “205 Cybersecurity Stats and Facts for 2026”, https://www.vikingcloud.com/blog/cybersecurity-statistics ↩︎
- Viking Cloud, “205 Cybersecurity Stats and Facts for 2026”, https://www.vikingcloud.com/blog/cybersecurity-statistics ↩︎
- Viking Cloud, “205 Cybersecurity Stats and Facts for 2026”, https://www.vikingcloud.com/blog/cybersecurity-statistics ↩︎
- Keeper Security, “Cybersecurity Disasters Survey: Incident Reporting & Disclosure” (September 2023), https://www.prnewswire.com/news-releases/keeper-security-releases-cybersecurity-disasters-survey-incident-reporting–disclosure-301938319.html ↩︎
- Simply Psychology, “Dark Figure of Crime” (November 2025), https://www.simplypsychology.org/dark-figure-of-crime.html ↩︎
- Peter Drucker, quoted in “15 Great Quotes About Questioning”, LinkedIn (March 2018), https://www.linkedin.com/pulse/15-great-quotes-questioning-joe-iarocci ↩︎